Survey on Cloud Computing Security
الكلمات المفتاحية:
Cloud Computing، Attacks، Security، Models، IDS، CIDSالملخص
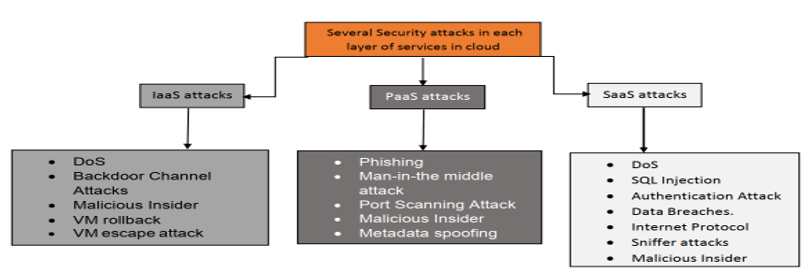
One of the most popular IT subfields today is cloud computing. With a simple Internet connection, it enables users to access cutting-edge information, technology, and infrastructure. Because of the numerous benefits offered, most international organizations have started to move toward cloud computing environments during the last few decades. Companies and organizations find cloud computing appealing because it eliminates the need to plan for provisioning and enables them to start with modest resources and progressively raise them as service demand increases. Cloud computing presents opportunities for research as well as obstacles. The security and privacy of data in cloud systems are important issues. Now that cloud computing technology is developing quickly, it is more convenient for businesses to move their workload there. It asks for a smaller investment and guarantees quick delivery of cutting-edge technologies. Cloud security is of the utmost importance. It is susceptible to cyberattacks that exploit its vulnerabilities in an insecure cloud environment. This puts the cloud environment’s assets, resources, and data in danger. In this paper, we reviewed some cloud computing studies about various attacks on cloud computing services. This paper’s main objective is to give readers a better understanding of security issues and solutions.
التنزيلات
منشور
كيفية الاقتباس
إصدار
القسم
الحقوق الفكرية (c) 2024 Fatima Ismail ALhadi, Nagi Ali AL-Shaibany, Sharaf Abdulhak AL-Homdyl

هذا العمل مرخص بموجب Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
